Security Tooling in Your DevOps Pipeline
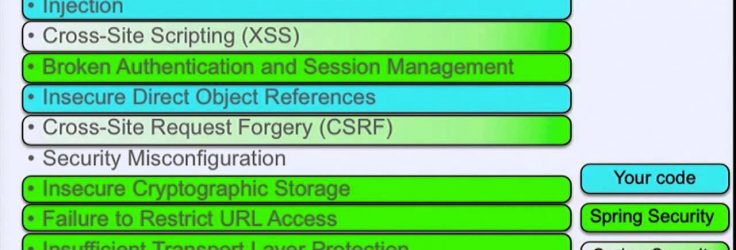
This talk explores how you can use tooling and automation to include security early on and throughout a continuous integration/continuous delivery (CI/CD) DevOps pipeline. Scanning the platform for vulnerabilities and the code for 3rd-party components with known vulnerabilities, using static code analysis and performing dynamic security testing are some strategies …